Configuration of Checkmarx (BYOR).
SAFE can integrate with Checkmarx by sending the vulnerabilities to the risk managament page.
Enabling Checkmarx
To enable the sending of scan results from SAFE to Checkmarx, add "checkmarx" to the list of outputs in the config.json
{
"output": ["stdio", "checkmarx", "file"],
"version": "1.1",
"project": {
"name": "appname",
"type": "beam",
"apps": [
{
"name": "appname",
"additional_includes": []
},
{
"name": "appname2",
"additional_includes": []
}
],
"paths": [
"_build/prod/lib"
]
}
}
Define the environment variables for Checkmarx API
In your CI/CD pipeline, define a job specifically for SAFE (e.g., security-check). For installation instructions see the Download page.
These are the necessary environment variables to allow results being sent to Checkmarx.
env:
SAFE_LICENSE: ${{ secrets.SAFE_LICENSE }}
CHECKMARX_API_KEY: ${{ secrets.CHECKMARX_API_KEY }}
CHECKMARX_PROJECT_ID: ${{ secrets.CHECKMARX_PROJECT_ID }}
CHECKMARX_TENANT_ACCOUNT_NAME: ${{ secrets.CHECKMARX_TENANT_ACCOUNT_NAME }}
CHECKMARX_REGION: ${{ secrets.CHECKMARX_REGION }}
Github actions
name: Erlang CI
on:
push:
branches: [ "main" ]
pull_request:
branches: [ "main" ]
permissions:
contents: read
jobs:
build:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- uses: erlef/setup-beam@v1
with:
otp-version: '26'
rebar3-version: '3.24.0'
- name: Compile
run: rebar3 compile
- name: Upload _build directory
uses: actions/upload-artifact@v4
with:
name: build-artifact
path: _build
security-check:
runs-on: ubuntu-latest
needs: build
container:
image: erlangsolutions/safe:1.1.0-otp-26
steps:
- uses: actions/checkout@v4
- name: Download _build directory
uses: actions/download-artifact@v4
with:
name: build-artifact
path: _build
- run: safe start
env:
SAFE_LICENSE: ${{ secrets.SAFE_LICENSE }}
CHECKMARX_API_KEY: ${{ secrets.CHECKMARX_API_KEY }}
CHECKMARX_PROJECT_ID: ${{ secrets.CHECKMARX_PROJECT_ID }}
CHECKMARX_TENANT_ACCOUNT_NAME: ${{ secrets.CHECKMARX_TENANT_ACCOUNT_NAME }}
CHECKMARX_REGION: ${{ secrets.CHECKMARX_REGION }}
SAFE_LICENSE: ${{ secrets.SAFE_LICENSE }}
- name: Persist results
uses: actions/upload-artifact@v4
with:
name: project-safe-results
path: _results/<<Project_Name>>.safe
The value for CHECKMARX_REGION can be one of these:
us,
us2,
eu,
eu2,
deu,
anz,
ind,
sng,
uae
The CHECKMARX_TENANT_ACCOUNT_NAME can be found in the Account Settings screen in the web portal.
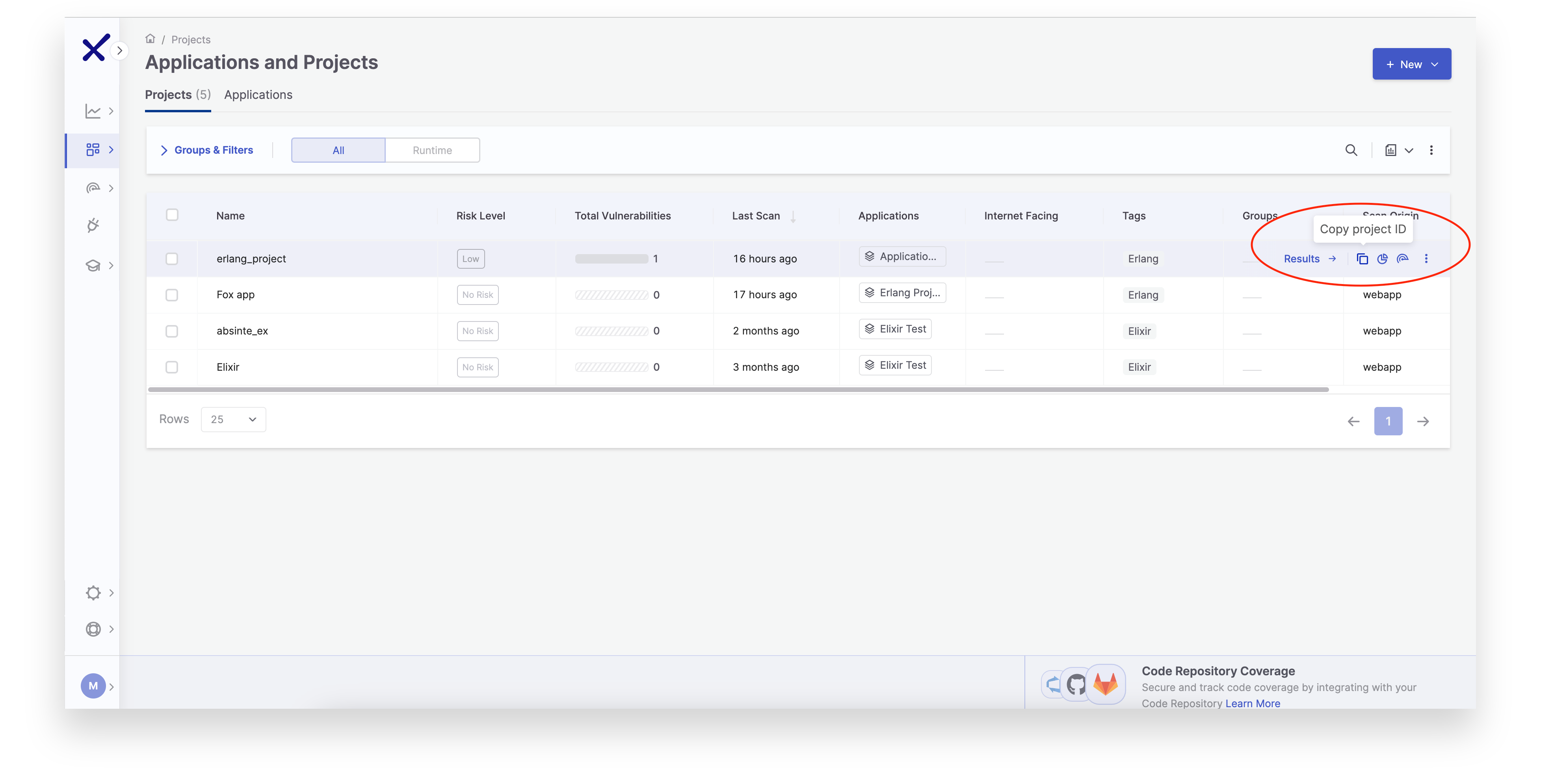
The CHECKMARX_PROJECT_ID can be found in the project page.
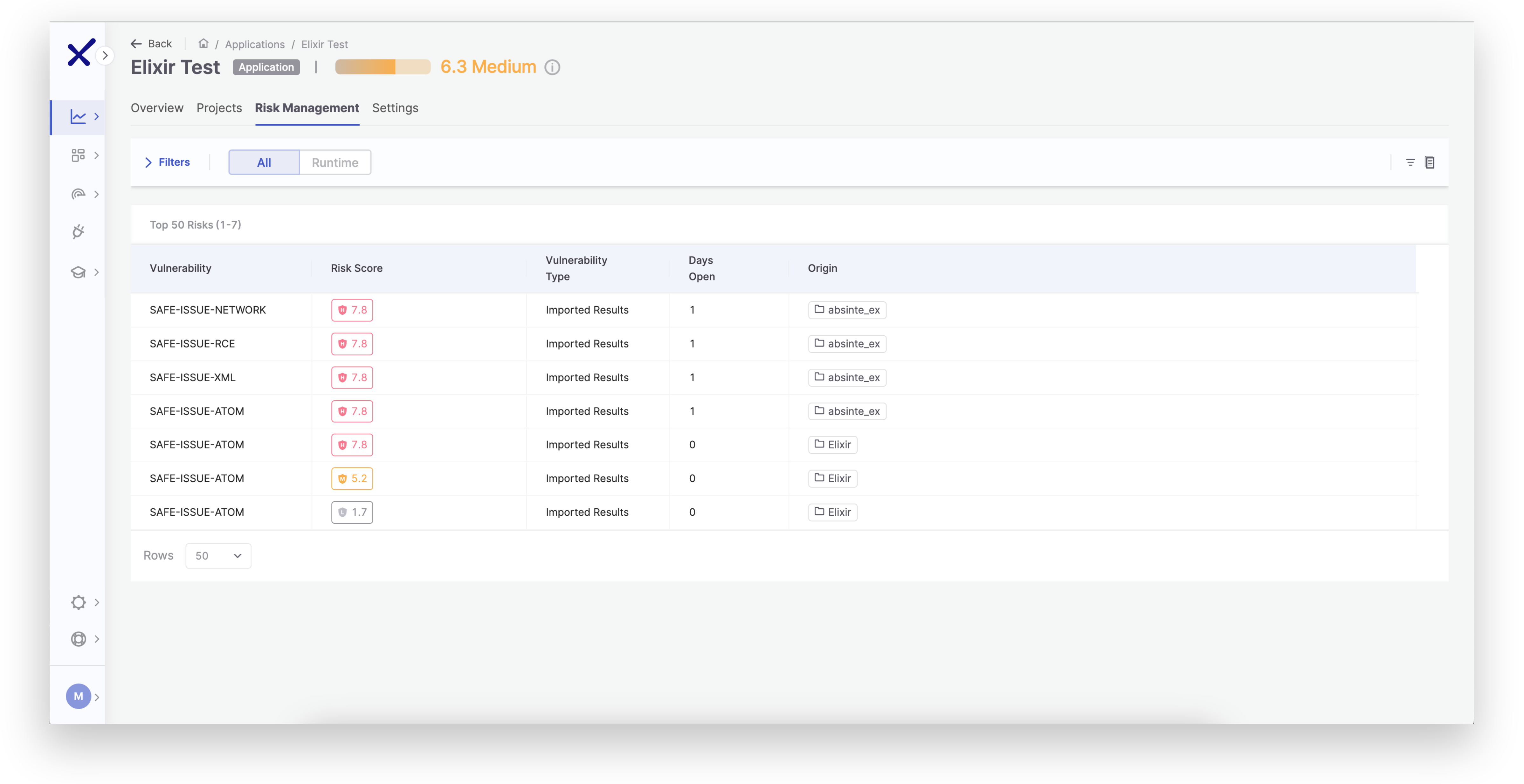
After the CI run, the results are sent to Checkmarx and will be created in the Risk Management page.
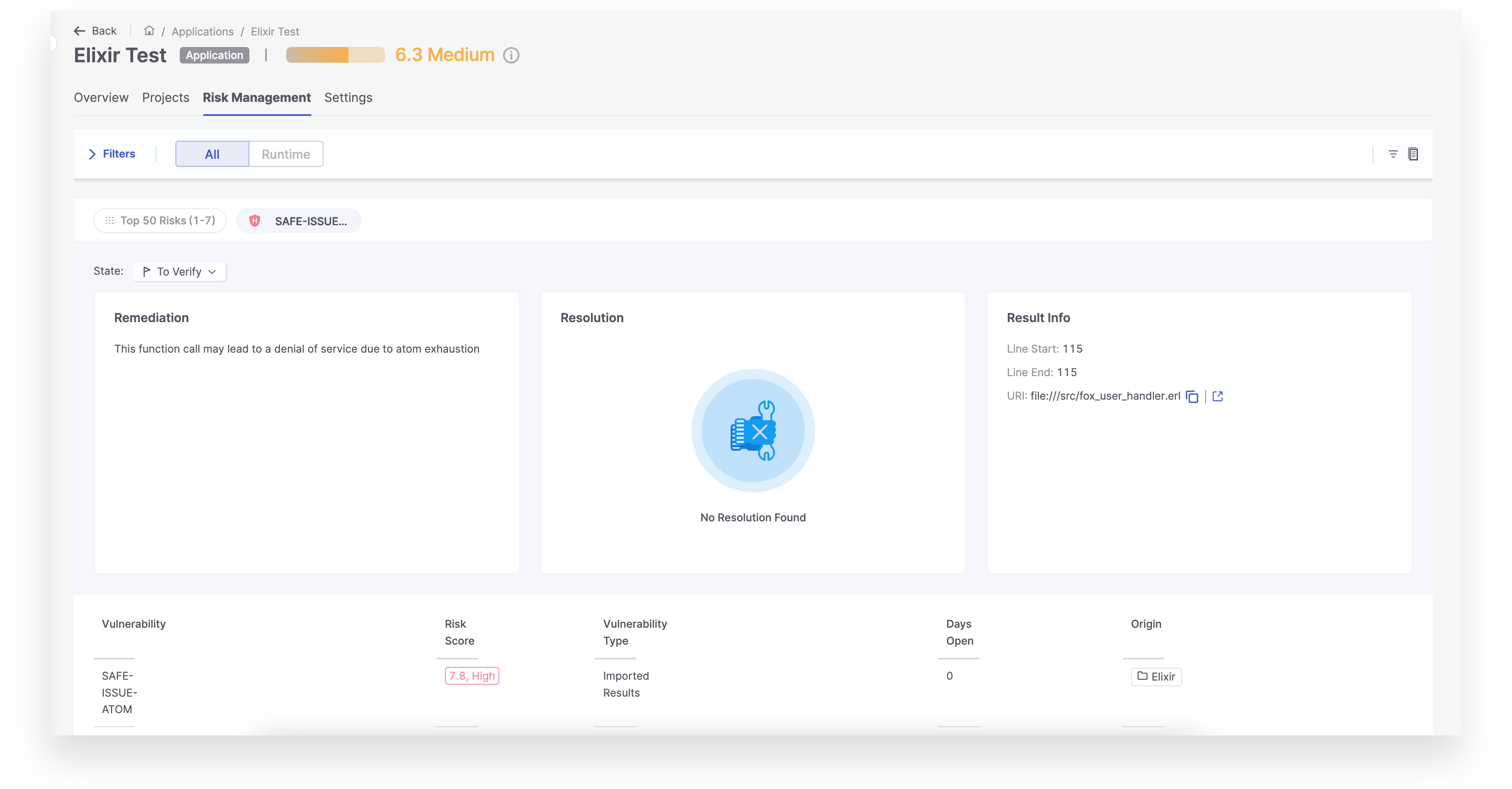
And the details for each vulnerability is shown.
SAFE SARIF Vulnerability Definitions
This outlines the vulnerability identifiers used by the SAFE static analysis tool in its SARIF output. Each identifier corresponds to a specific class of security issue or software risk in Erlang/Elixir systems.
Deprecation & Removal
These issues indicate use of functions or patterns that are deprecated or removed in current or upcoming OTP releases.
| ID | Description |
|---|---|
SAFE-ISSUE-DEPRECATED | This call is either deprecated or will be deprecated in the future. |
SAFE-ISSUE-REMOVED | This function call was deprecated. |
SAFE-ISSUE-REMOVED-OTP19 | Deprecated in OTP 19. |
SAFE-ISSUE-REMOVED-OTP20 | Deprecated in OTP 20. |
SAFE-ISSUE-REMOVED-OTP21 | Deprecated in OTP 21. |
SAFE-ISSUE-REMOVED-OTP22 | Deprecated in OTP 22. |
SAFE-ISSUE-REMOVED-OTP23 | Deprecated in OTP 23. |
SAFE-ISSUE-REMOVED-OTP24 | Deprecated in OTP 24. |
SAFE-ISSUE-REMOVED-OTP25 | Deprecated in OTP 25. |
SAFE-ISSUE-REMOVED-OTP26 | Deprecated in OTP 26. |
SAFE-ISSUE-REMOVING-OTP27 | Will be deprecated in OTP 27. |
SAFE-ISSUE-REMOVING-OTP28 | Will be deprecated in OTP 28. |
Code Execution & Injection
These issues represent high-risk patterns where user input can potentially lead to arbitrary code execution.
| ID | Description |
|---|---|
SAFE-ISSUE-OS | Unverified system command execution can lead to injection attacks. |
SAFE-ISSUE-PORT | Unsafe port creation can result in injected malicious code. |
SAFE-ISSUE-PORT-DRIVER | Poor input validation in port drivers may allow malicious injection. |
SAFE-ISSUE-NIF | Unsafe Native Implemented Functions (NIFs) can lead to code injection. |
SAFE-ISSUE-COMPILE-LOAD | Dynamic code compilation/loading from unvalidated sources. |
SAFE-ISSUE-FILE-EVAL | Evaluating code from files without input validation. |
SAFE-ISSUE-FILE-READ | File operations without validation may allow DOS or injection. |
Denial of Service (DoS)
These issues may exhaust system resources or crash the VM when exposed to attacker-controlled input.
| ID | Description |
|---|---|
SAFE-ISSUE-ATOM | May lead to atom table exhaustion (permanent memory leak). |
SAFE-ISSUE-XML | Unsafe XML parsing can trigger atom exhaustion or crash. |
Web & Remote Exploits
These cover security issues in network-facing or browser-facing interfaces.
| ID | Description |
|---|---|
SAFE-ISSUE-XSS | Cross-site scripting (XSS) vulnerability. |
SAFE-ISSUE-PHX-SEND-RESP | Unvalidated input to Plug.Conn.send_resp/3 may allow XSS. |
SAFE-ISSUE-RCE | Remote Code Execution (RCE) vulnerability. |
System-Level & Distributed Risks
Vulnerabilities tied to concurrency, process control, or distributed system configuration.
| ID | Description |
|---|---|
SAFE-ISSUE-PRIORITISATION | Custom priorities can destabilize the scheduler (starvation, deadlocks). |
SAFE-ISSUE-LINKING | link/1 used for remote connections may crash if the target dies prematurely. Prefer spawn_link/1-4. |
SAFE-ISSUE-ETS-CALLS | Unsafe parallel mutations of ETS tables during traversal. |
SAFE-ISSUE-NETWORK | Erlang node access allows arbitrary remote access if misconfigured. |
SAFE-ISSUE-COMMUNICATION | Using outdated TLS/SSL (3.0, 1.0) risks MITM and data tampering. |
Cryptographic Issues
Incorrect or outdated use of cryptographic primitives.
| ID | Description |
|---|---|
SAFE-ISSUE-CRYPTO | Use of obsolete or unsafe low-level crypto functions. |